Video
Operation RoundPress targets webmail software to steal secrets from email accounts belonging mainly to governmental organizations in Ukraine and defense contractors in the EU
15 May 2025
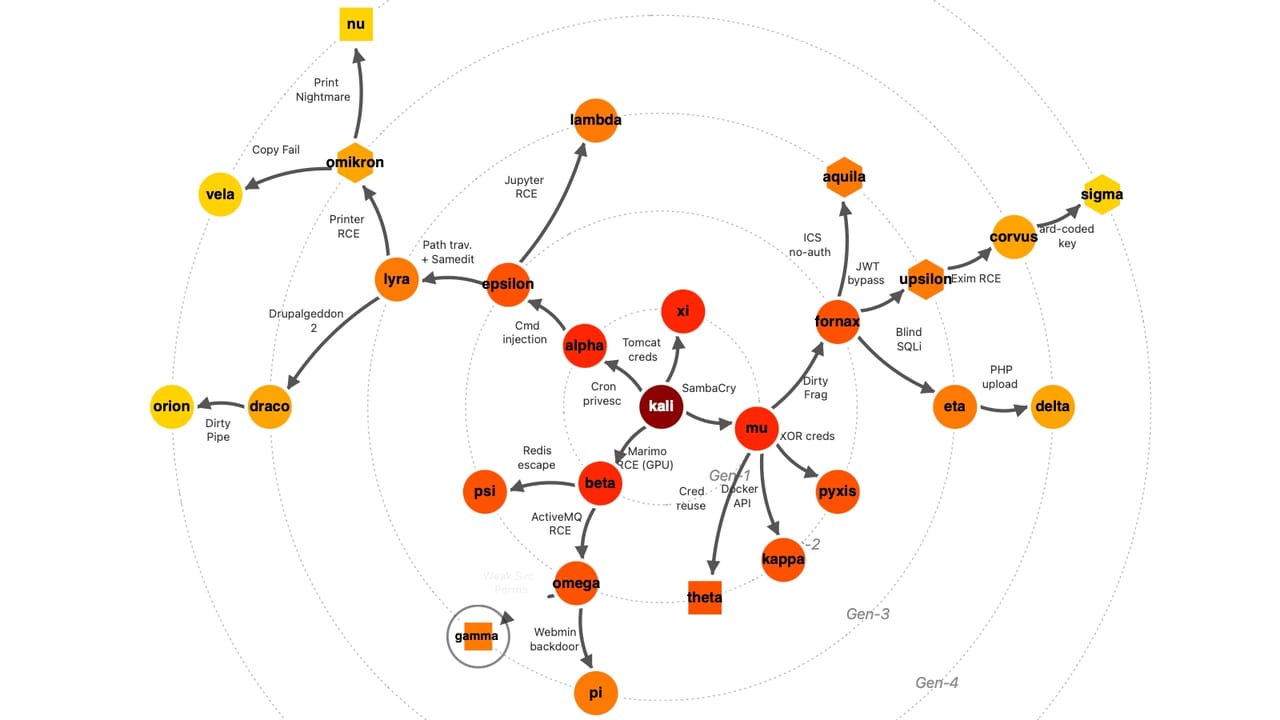
ESET researchers have discovered a cyberespionage operation that abuses cross-site scripting (XSS) vulnerabilities, including a zero-day XSS flaw in MDaemon webmail software, to steal confidential information from specific email accounts belonging to officials working for various governmental organizations in Ukraine and defense contractors in Europe and on other continents.
Operation RoundPress, so nicknamed by ESET, is most probably the work of the Russia-aligned Sednit APT group, who first took aim at Roundcube, but later expanded its targeting to other webmail software, including Horde, MDaemon, and Zimbra. In some cases, the attackers even circumvented two-factor (2FA) authentication.
What else is there to know about the operation’s tactics, techniques, and procedures? Learn from ESET Chief Security Evangelist Tony Anscombe in the video and make sure to read the full blogpost.
Let us keep you
up to date
Sign up for our newsletters


.jpg)







.png)

.jpeg)
